API Management: Everything You Need To Know
It’s estimated that the API management market will be valued at $5.1 billion by 2023.
Google, GitHub, Spotify, Facebook, and several other tech platforms have created systems that encourage developers and marketers to exploit their data via APIs.
In the 19th Developer Economics Survey Report that was published by Slashdata, it was revealed that nearly 90% of developers are leveraging APIs in some capacity.
Well-composed REST APIs have become a trend for innovative tech transformation — and it’s high time you tap into this huge opportunity.
In this ultimate guide, we’ll learn everything about API management, and how API provides a reflective interface to help developers communicate with data.
We’ll also introduce you to what API keys are, how API integration works, RESTful API best practices, and how to secure API.
What is API Management?
According to Amazon Web Services:
“Application Programming Interface (API) management consists of a set of tools and services that enable developers and companies to build, analyze, operate, and scale APIs in secure environments.”
The perfect API management tools and platforms help in the process of distributing, controlling, and efficiently analyzing the APIs that connect different applications and data across the enterprise and the clouds.
What is an API?
API (Application Programming Interface) is a standard way to get information and software capabilities from a third-party provider.
APIs are an important part of modern software development because they allow companies to tap into more sophisticated software and information without spending a fortune.
For example, a food truck owner may want to aggregate data from Twitter into Google Sheets. To accomplish this, they commission developers to write an API for his truck.
Almost all social media platforms and software have their native APIs. Facebook, for example, has one of the most useful APIs — which allows two or more websites to share data.
Interestingly, Advertisers can retarget their customers using the Facebook Conversion API.
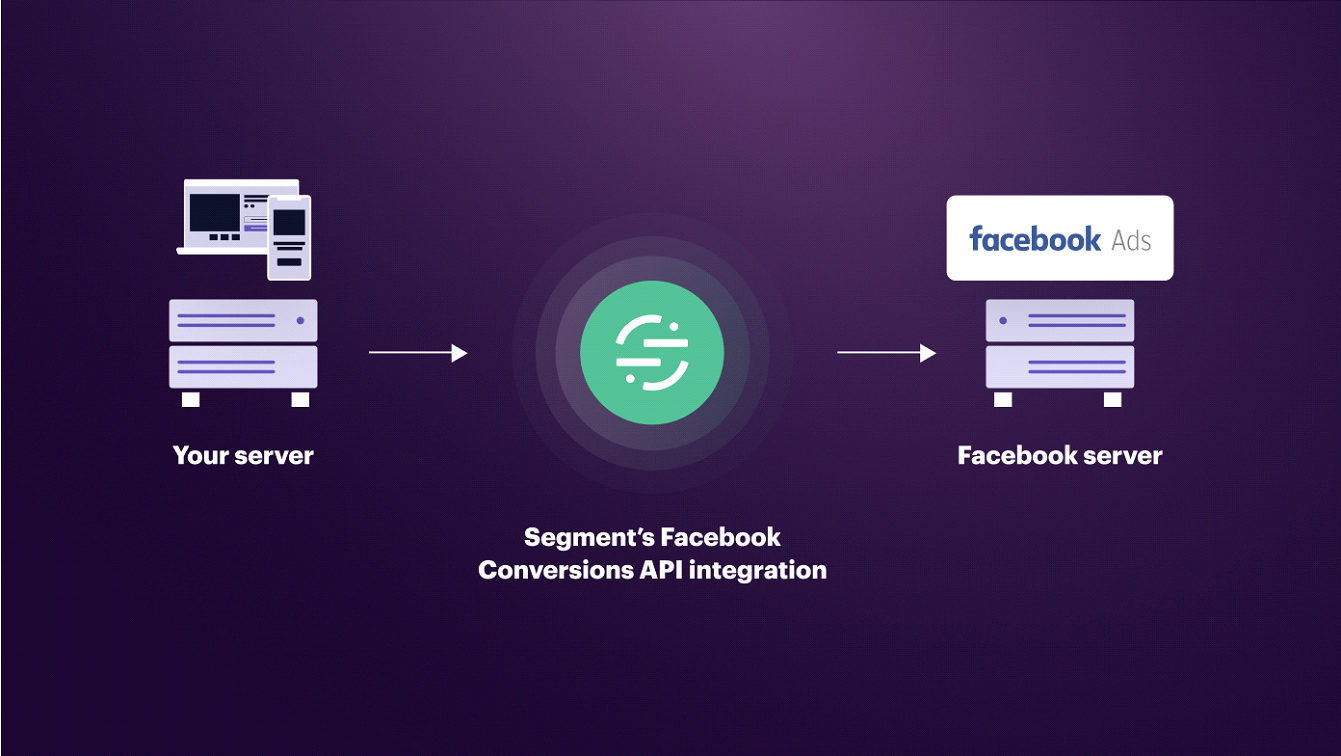
Have you ever logged into another website just by clicking on the Facebook login link? That’s an API bridge.
APIs are everywhere and have many faces. Your car navigation system can send you to the airport using a map provided by Google, and it even charges you for using that data.
Even share buttons on websites are APIs as well — which enable users to share content with their friends on Facebook, Instagram, Twitter, LinkedIn, etc.
In addition to the internet, APIs are used to simplify the workflow of software programs.
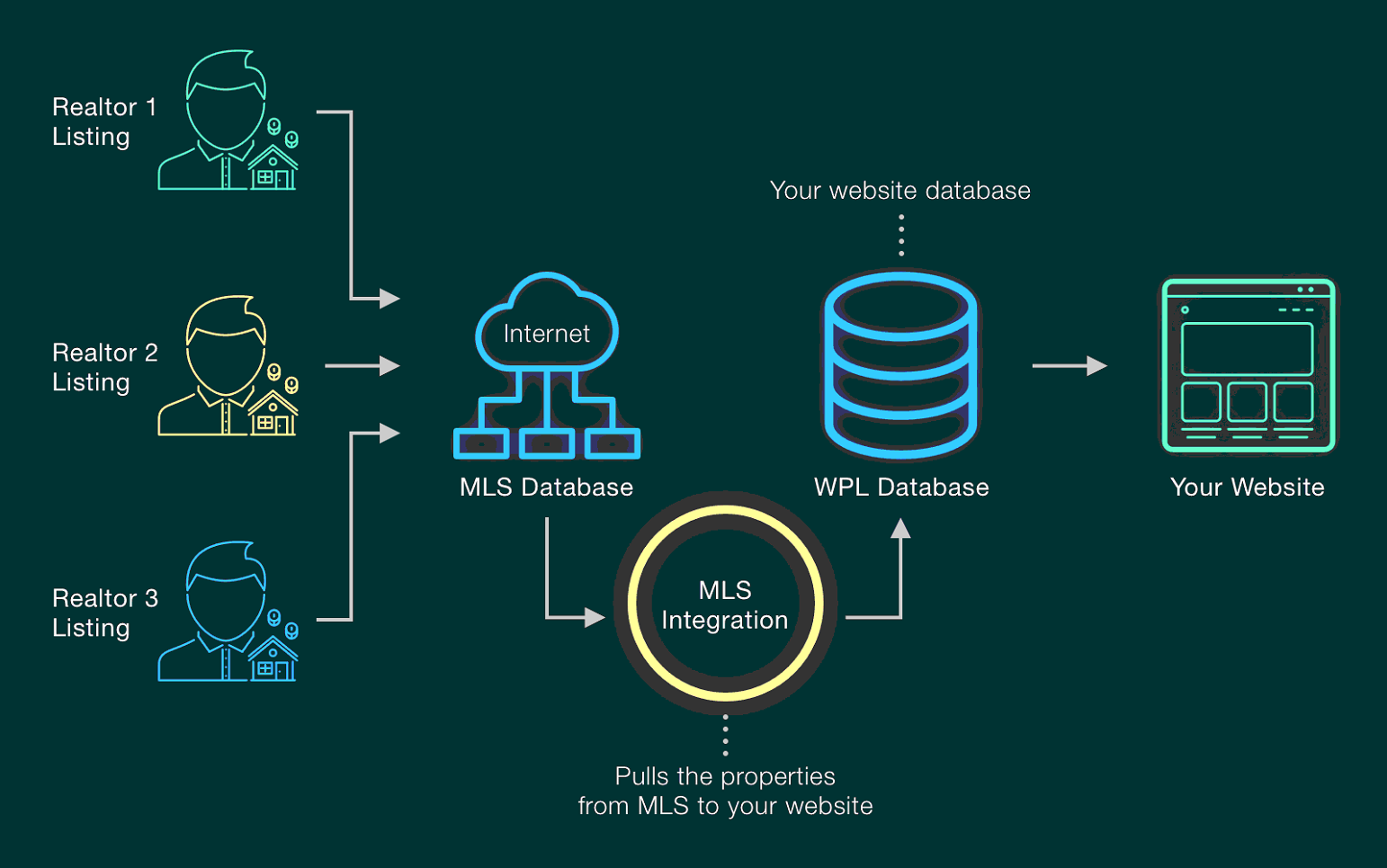
For example, a real estate website might have multiple APIs for property listings, showing the availability of properties.
For a small business, an API could make it easier for customers to book appointments.
A customer could enter a request for an appointment and then the website would automatically create an event in Google Calendar.
This example can be extended to include many other applications as well.
Why is an API Needed?
What are the key benefits of API and why are they needed in today’s business world? Here are the 3 primary reasons:
1) APIs Assist in Data Management
APIs can help you manage your business information more effectively. Using an API can improve your data management by ensuring that data is shared and accessed accurately.
Here’s a detailed example of a Framework for Organization Data Management using API.
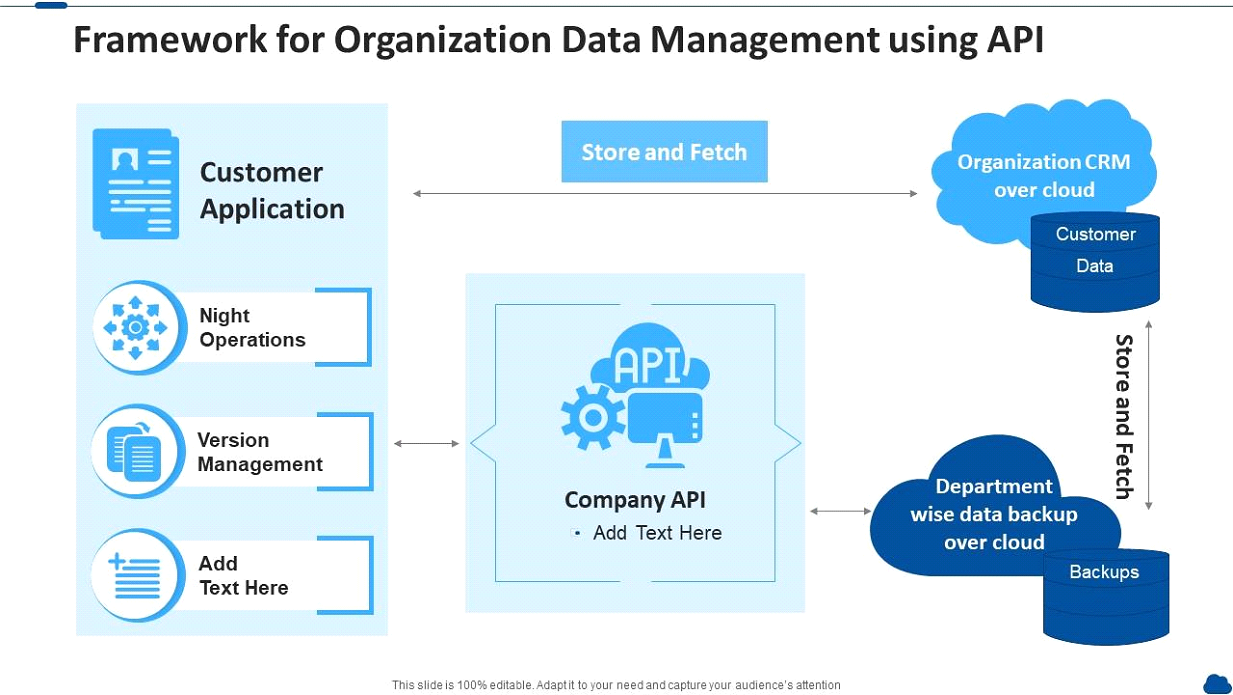
An API provides a set of rules and functions that describe how applications can interact with each other.
It acts as an intermediary layer between two systems and can support data migration faster and improve data quality. It also allows you to offer more flexibility when providing services.
You can use an API to access external data sources, as well as connect to databases from a variety of platforms. These benefits are just a few of the many ways APIs can help you.
Data-driven organizations benefit from API management. Companies can use it to expose and make their assets available through apps.
API management helps organizations manage and scale their APIs while providing developers with the security and privacy they need.
2) APIs Create Partnerships with Other Companies
APIs provide an opportunity to leverage the power of open data and a new ecosystem of partners.
The business value of a platform depends on its ability to serve unique customer needs. APIs allow organizations to integrate their software systems with other companies’ solutions.
APIs provide a foundation for this goal and open the door to new revenue streams.
But how can APIs be used to support customer ecosystem growth? Let’s explore how these technologies can benefit your business.
APIs help enterprises compete with bigger players.
Small businesses can leverage the power of big enterprises by developing APIs — since they are far smaller than fully-developed applications.
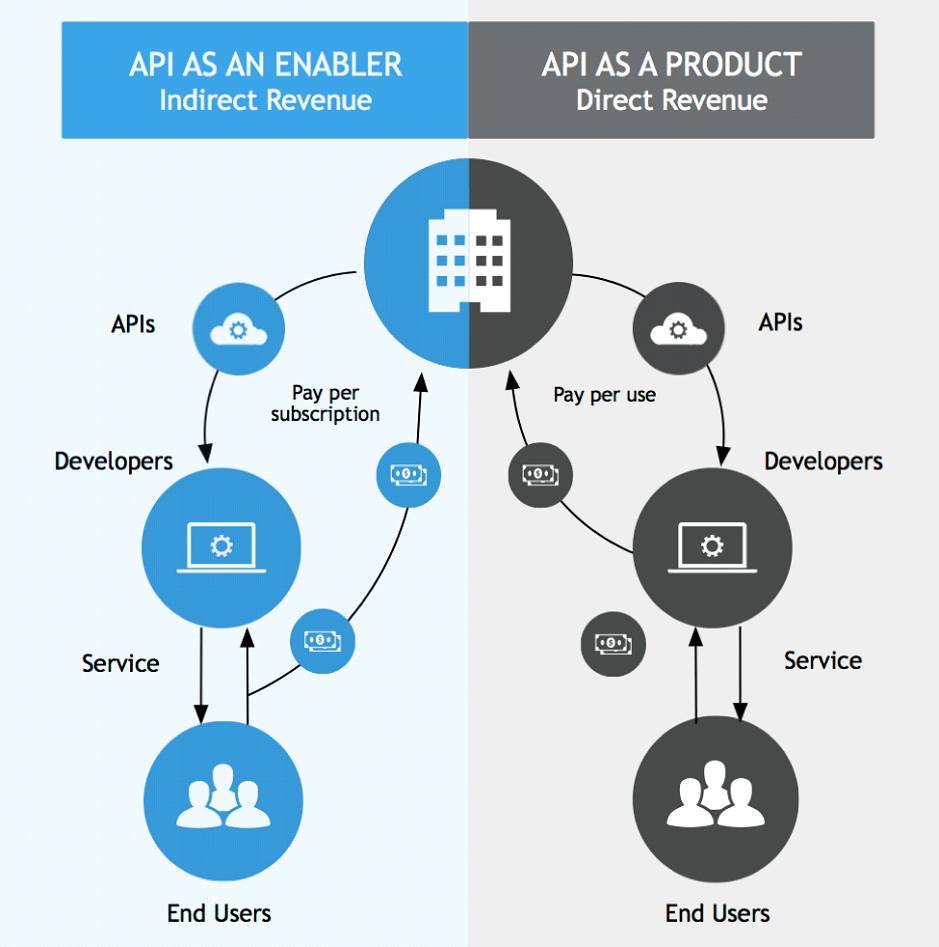
3) APIs Promote Business Growth
A well-developed API can help institutions generate massive amounts of value. But, to maximize the value, institutions need to understand the most effective ways to use them.
Leaders in the field of API use analyze potential API destruction and creation and the corresponding impact on revenue, customer experience, and productivity.
To identify opportunities, institutions should take the customer’s journey into account.
In one case, a bank pulled technology and business professionals into a joint team to identify APIs that address customer pain points.
API providers can respond quickly to customer demands and new business opportunities.
APIs also enable businesses to build and extend a 360-degree view of their customers. With these benefits, APIs promote business growth.
They are increasingly used by many different types of companies.
What Are The Different Kinds of APIs?
APIs power today’s vast software ecosystem. If you want to connect your service or app to the digital space, it’s important to embrace APIs.
Most developers and marketers use Web APIs that are accessed via the Hypertext Transfer Protocol (HTTP), which is also helpful for fetching and serving web pages in browsers.
There are 4 main types of web APIs, let’s explore them:
i) Open APIs?
An open API is a publicly accessible resource that offers programmatic access to software, usually a proprietary stack or open-source software.
Open APIs are a great way to share data and content across web communities.
Some examples of these resources include geolocation, stock quotes, and tweets. In some cases, an open API can be used to interact with a single entity, such as a company.

However, you must be careful when making changes to these resources.
Changing them could result in dissatisfaction from end users, and sullying the reputation of the organization that provides the public API.
A major benefit of open APIs is their versatility. Developers can use them to create apps and services for many industries.
ii) Partner APIs
Partner APIs are applications that allow companies to share information with other businesses.
This model is becoming increasingly popular as more businesses seek ways to streamline the sales process, as well as provide customers with new features and functions.
For example, Shopify offers tools for eCommerce websites, and by offering Partner Dashboard access, API partners can automate front and back-office operations.
As partner APIs evolve and get better, the ultimate goal is to help developers have easy access to cash, as predicted by Matt Bahr in response to a tweet from Shopify’s Director of Engineering — Derek Watson.

In theory, this model makes sense – one developer for all departments? After all, he or she could handle sales, marketing campaigns, customer support, and more!
But in reality, that’s not how software development works. Instead, it would be better to design your API first and then pass it on to your partner.
iii) Internal APIs?
If you’re not familiar with the concept of internal APIs, here’s a quick overview of what they are and how they can benefit your business.
Internal APIs are standardized, and accessed by internal developers, and they offer a flexible way to integrate different IT systems.
Because the interfaces are hidden from the public, they simplify application development processes.
Furthermore, they let developers reuse internal software assets and save time and money.
iv) Composite APIs?
There are different flavors of composite APIs. These APIs offer different ways to achieve the same thing.
For example, a composite batch may execute up to 25 separate sub-requests in one request.
Each sub-request executes serially and independently.
Here’s an example of a composite request in Salesforce whereby a contact object is associated with an account object for an individual:

Each sub request may be a JSON or XML object, and the URL for a composite batch will include the API version composite, followed by several of subrequests.
A composite response structure will echo the structure of the request.
It includes a top-level success field and an object containing a sequence of individual responses.
What is a REST API?
REST stands for Representational State Transfer. RESTful API is a service that enables developers to interact with a server using a simple URL.
It uses HTTP requests and responses to exchange data.
The underlying model is client-server and relies on resources to communicate between the server and the client.
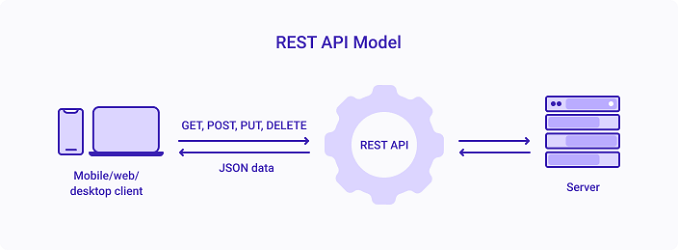
This makes it easy for developers to display information on the client side while storing and manipulating data on the server.
A client is a program or person who requests a particular resource. For example, a web resource may be anything the client interacts with on the Internet.
An API may return a URL or an executable piece of code, such as Java applets. The server will respond with a JSON, XML, or text based on the client’s requests. The client can then interpret the data.
The underlying client-server architecture is very similar to that of a Web service and allows for a uniform user interface for the client and server.
Despite this, however, it’s possible to separate the server and client. The separation of the server and client also facilitates portability across platforms and increases scalability.
What is an API Gateway?
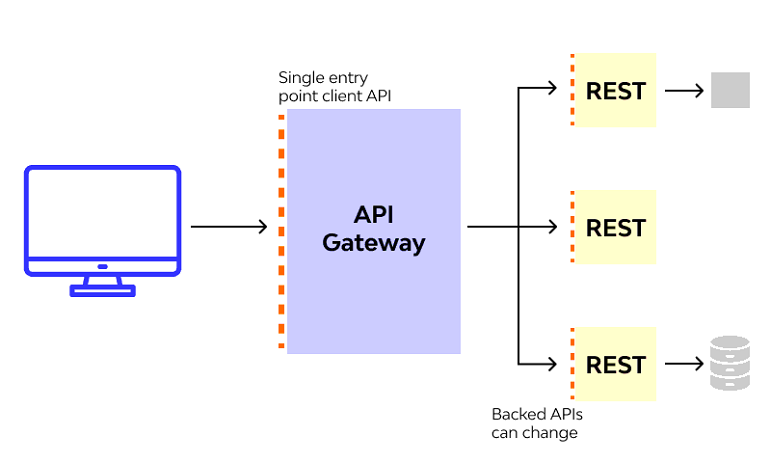
An API Gateway is a platform that lets your application connect to a backend service to perform various functions. It helps maintain security policies and balances API invocation at runtime.
The API gateway also provides great performance, scalability, and availability for your application.
If you’re looking for a solution to architectural complexity, an API gateway could be just the thing for you.
As API gateways are critical to any application, choosing the right one is critical.
While implementing an API gateway can be difficult, testing all options can ensure success. You can use different providers for different groups of microservices.
Alternatively, you can create your own API gateway. Allegro, for example, built its own API gateway — “to make API calls a seamless experience,” says Pawel Wolak.

An API gateway can be either open source or proprietary. Open source API gateways are free but are often extensible and customizable.
They are typically open source and have plugins that you can use to extend their functionality. Regardless of the type of API gateway you use, there are many options for implementing and managing your API.
Why API Gateways are Required
API gateways are required for many different reasons, including scalability, availability, fault tolerance, and shared state.
They should also provide linear scalability, replicate across multiple data centers, and reduce latency for consumers.

API gateway must know where each microservice is located.
While traditional architecture hardwires the location of each service, cloud-based microservice applications use dynamic location to accommodate auto-scaling and upgrades.
These gateways are essential to API-driven architecture. They help businesses innovate quickly by integrating with best-of-breed external services.
They also help them deliver new services faster. With so many benefits, APIs have become essential to running a business.
An API gateway provides an extra layer of security and control for the APIs, ensuring the data is secure, available, and scalable.
What Are API Keys?

API keys are used to connect applications with data. APIs can be found in many places, from Google Maps to Amazon Web Services.
These APIs are mostly free while some may require a fee for an agreement. More applications use APIs to integrate data from other sources.
APIs are so ubiquitous that it is hard not to see them everywhere. For example, Google Maps provides address and location data.
An API key is a key to access this data, and API providers typically provide a URL for the user to input.
To better design APIs that will be easy to use, there are best practices and standards to follow, here are 4 of them:
1) Send and Receive Data API Calls With JSON
Using JSON as the standard for sending and receiving data API requests can make your life easier. If you want to use JSON for API calls, here are a few tips:
To utilize JSON for API calls, you should be familiar with the format of JSON.
Use a header called Content-Type to indicate the format of the data. For example, application/json would indicate JSON data.
A good example is how Python provides json.loads() and json.dumps() for working with JSON data.
Set the Content-Type type in the response header to application/json while making the request — to ensure the client interprets JSON data correctly.
Also, use a URL for the resource. It is important to include a single resource object as the primary data in any request.
2) Manage Error Handling With Status Codes
You can use Status codes in error handling for your API to help your users understand what is going wrong.
HTTP status codes are short descriptions of longer messages, which indicate whether a request succeeded or failed.
This table illustrates the different HTTP Status Code ranges and their meanings:
| Status Code Range | Meaning |
|---|---|
| 100 – 199 | Informational Responses. For example, 102 indicates the resource is being processed |
| 300 – 399 | Redirects For example, 301 indicates “Moved permanently.” |
| 400 – 499 | Client-side errors 400 is a bad request and 404 means resource not found |
| 500 – 599 | Server-side errors For example, 500 indicates an internal server error |
You can also include the title text to let consumers know what the error caused. Keep in mind that status codes are not a substitute for error messages.
You should try to use them as helpful messages. If you’re unsure how to write them, read the following article.
You must use error codes that convey context. For instance, if the response contains a 400 Bad Request, you should not give the user a 404 error message. Instead, include a detailed description of the error.
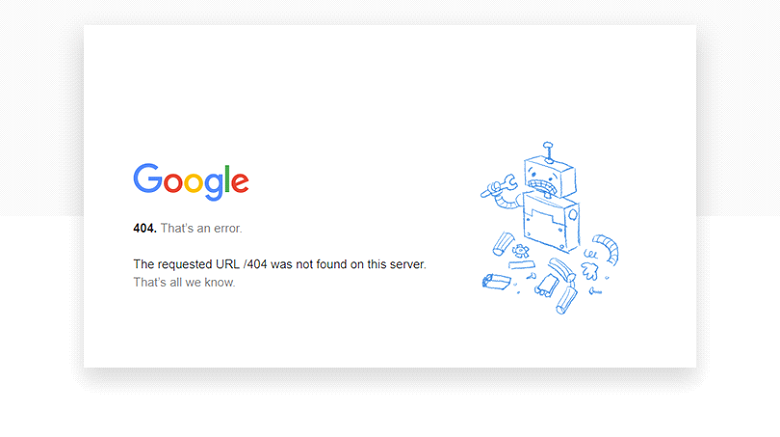
The response body should also include the error code. It should also be written in the language of the request.
The 400 Bad Request error code is a good example of a code that conveys the context of the request.
3) Call Endpoints With Nouns Instead of Verbs
The most obvious reason to avoid using verbs in your API’s endpoints is that they’re confusing to users. Instead, use nouns to make it easier for users to remember.
Verbs, while technically acceptable, are too confusing. Using %20 for “space” is also not the best idea, as it violates the naming convention.
In addition, %20 characters are encoded to prevent confusion and security problems.
Verbs tend to be more rigid because they’re tightly coupled to specific actions.
HTTP Action Verbs, on the other hand, allow for loosely coupled resources. GET, POST, and PUT are all examples of HTTP Action Verbs. And because they’re flexible, they can be added at any time.
It’s better to use an endpoint that looks like this: https://mybrandsite.com/posts
Instead of these: https://mybrandsite.com/getPosts or https://mybrandsite.com/createPost
If you want to make it more flexible, you should consider using nouns in your endpoints. You’ll be happier with the results.
4) Use Plural Nouns for Name Collections

One of the fundamental principles of API design is the use of proper naming conventions.
While using abbreviations and other grammatical structures is permissible, API names should be purely descriptive and make sense.
For example, using direct nouns such as the name, description, and ID is more logical than using fn or abbreviations such as API, Resource, or Method.
While it’s fairly easy to delete a post with a DELETE request or update a post with a PUT or PATCH request when you have an endpoint that looks like this:
https://mycompanysite.com/post/567, however, the user would be confused because they don’t know if there are other posts in the collection.
So you should always use plural nouns in your collections.
For example, use https://mycompanysite.com/posts/567 instead of https://mycompanysite.com/post/567
If nouns are identical in plural and singular forms, it forces the code to use the correct form. Generally speaking, naming conventions should be used consistently to avoid confusion.
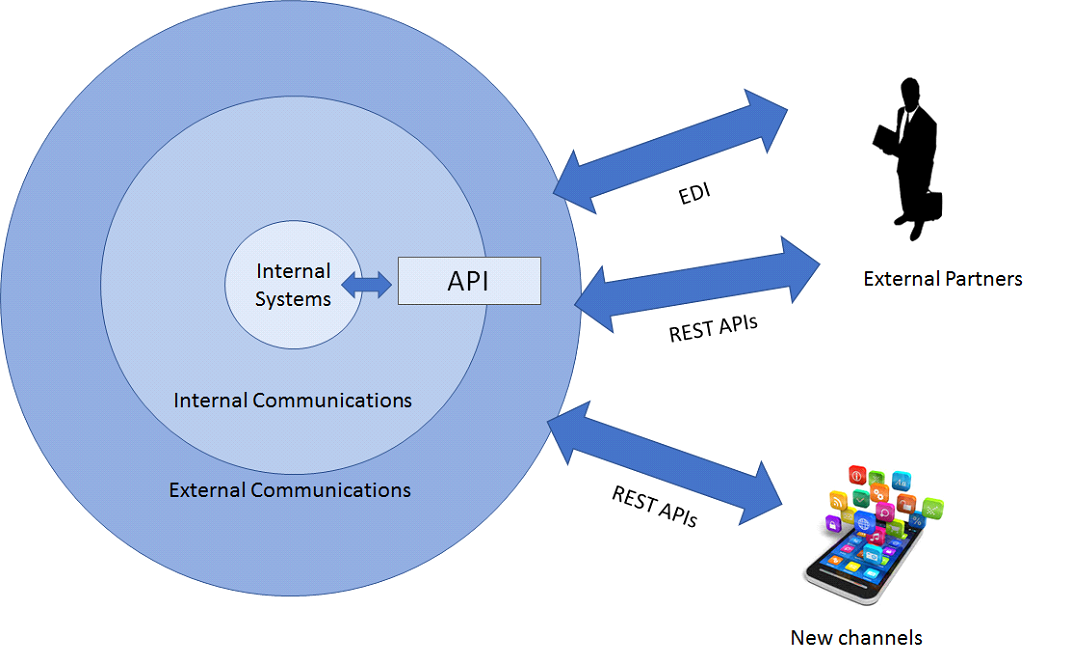
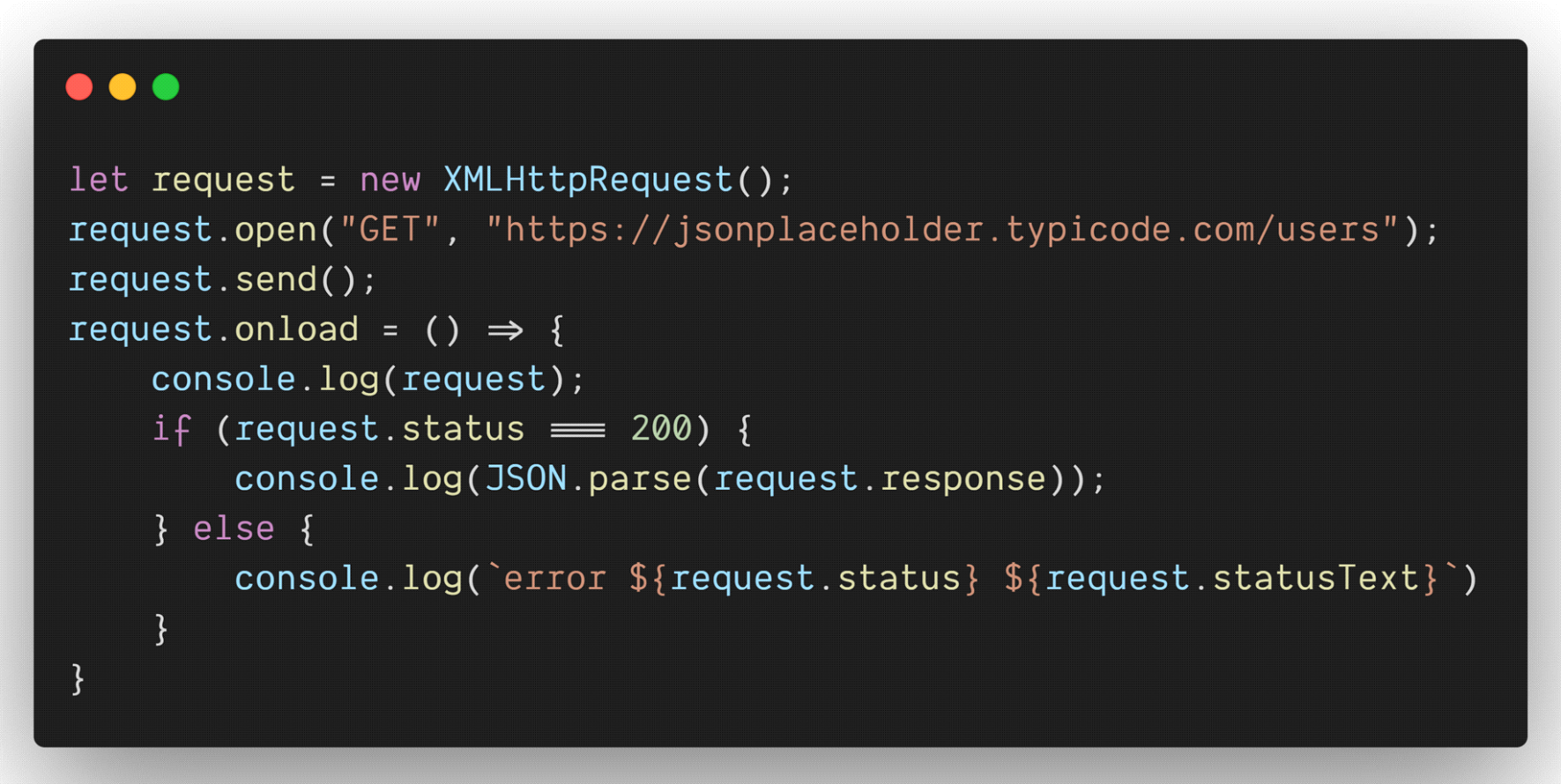
How Does API Integration Work?
APIs are the communication interfaces between systems. They allow users to send requests and receive data from different applications.
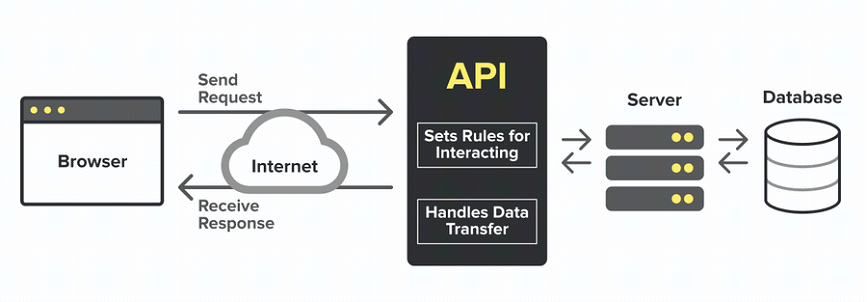
API integration works by setting rules for interacting with a sent request from the browser and forward it to the server, and the database. APi also handles data transfer and sends a response back to the browser.
Here’s an illustration from Alex Trost to explain API integration better:
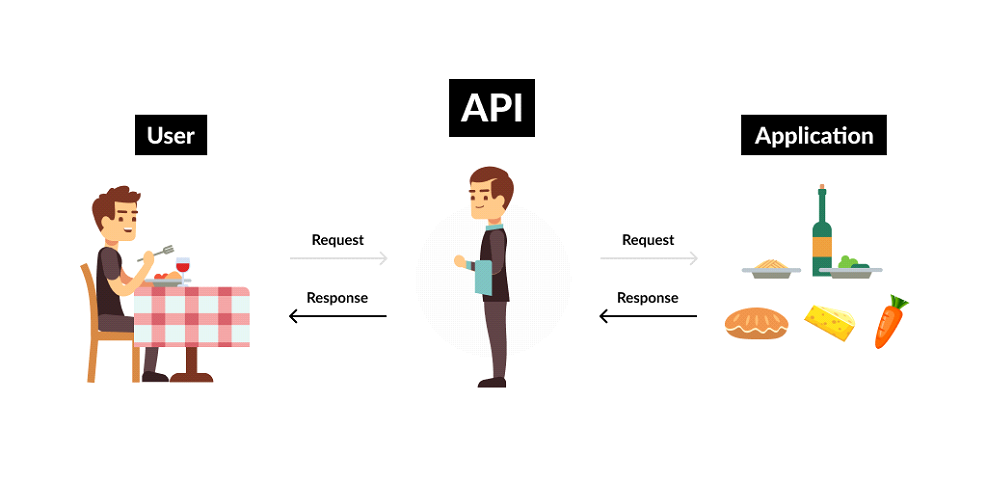
The process of API integration is often explained in metaphors.
For example, imagine a restaurant. The waiter will deliver an order to the kitchen and then return it once the food is ready.
The kitchen employees will then prepare the food. After that, the client will receive their meal. Let’s illustrate this concept better with how UberEats API works:
When integrating systems, it’s important to identify the pain points. The integration process begins with identifying the pain points, which can include new features or improved performance.
Developers should also identify the objectives of the integration process. Once these goals are determined, the development process can begin.
API integration platforms can provide a variety of features that other systems may not be able to offer. Testing is another important step in the integration process.
To use an API, you must register with it. Many APIs will require an account or unique key to access their data.
This helps prevent misuse of the service and ensures that only a specific application can access the requested data. Additionally, you can use an API that allows you to authenticate users using a secret key.
In the end, you’ll end up with a smooth integration process that will improve the performance of your web app.
How Do API Keys Work?
This section will explain clearly how API keys function. The process starts by generating an API key.
The key will be encrypted with the secret identifier provided by the requestor. Once generated, the key will be sent through a secure hashing algorithm.
Keep in mind that the user makes all the requests that trigger the API to act.
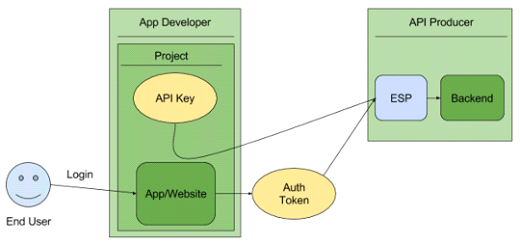
The resultant value is called a signature, and this signature is then placed in the header of the request.
When the API requester makes a request, the server will check the key against the id provided by the requestor. If the keys are different, a hacker will immediately realize the id and send the request back.
The process to acquire an API key is simple. First, you must register with the API owner.
Next, you must navigate through the API console documentation page to obtain your API key.
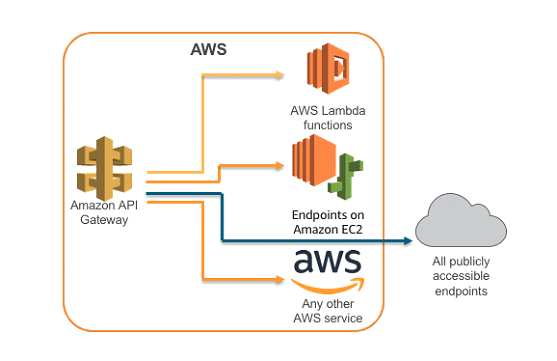
Many platforms use API keys for various purposes, including Amazon Web Services (AWS) and Google maps.
AWS uses API keys to bridge its private Endpoints, as shown below:
Government entities and healthcare organizations also use API keys. A key is required to use an API, and it is important to read the documentation carefully.
The API owner will publish the process for acquiring an API key.
API keys are a common tool for connecting applications and data. Amazon Web Services offers a series of APIs for managing its back-end servers.
These APIs are available to anyone and while using them is free, you must sign a contract to use the services.
The number of applications that use API keys is growing. Google Maps, for example, is widely used and provides address and location data. The same can be said for many other applications.
Are APIs Secure?
APIs are typically secure. However, there may be some threats to its security. To prevent security incidents, API developers need to implement many layers of protection.
This guide will help you understand what you should and shouldn’t do.
Here are some important things to know about APIs security:
a) APIs Rely on Strong Security Measures
APIs are secure when the proper security measures are in place.
Experian, for example, takes security seriously. APIs used for data requests are encrypted using OAuth and channel encryption.

Furthermore, APIs promote rapid evolution and innovation. However, they’re still a new technology that’s only been taken up by a few companies in the business world.
b) APIs are Prone to Attacks
APIs are easy targets for bad actors. They’re expected to become the top attack vector by 2025.
According to BrightSec, “APIs may have vulnerabilities such as code injection, lack of rate limiting, broken authentication and authorization, and more.
Organizations must test APIs regularly to identify vulnerabilities, and address them using security best practices.”
They play an essential role in digital transformation and offer external customers access to internal systems and sensitive data.
For this reason, APIs deserve a dedicated approach to compliance and security.
c) APIs Are Network-exposed
API security requires a culture of security. APIs are network-exposed, so it’s important to have security controls in place.
Authentication, authorization, and data context are among the most important components of API security.
Essentially, application security programs must capture and apply these activities whenever appropriate.
For API security to be effective, API developers must first have a culture of security. A culture of security is the best way to protect the APIs that provide them with critical services.
Best Practices to Secure APIs
While Employing mitigation measures (such as credential stuffing and Man-in-the-Middle) are useful, let’s explore a few more effective best practices to secure APIs.
1) Use SSL for Security in API Design
To ensure security, it’s crucial to use SSL for API design.
The Secure Socket Layer (SSL) protocol process starts with a valid SSL certificate, which is proof that the server and web browser are communicating securely.

To get an SSL certificate, you can coordinate with a trusted Certificate Authority (CA), such as DigiCert or Comodo.
The server and client then exchange a digital certificate with an associated private key.
2) Inventory and Manage Your APIs
Using inventory APIs can help you track inventory more efficiently and streamline processes.
See how the Azure API management platform works:
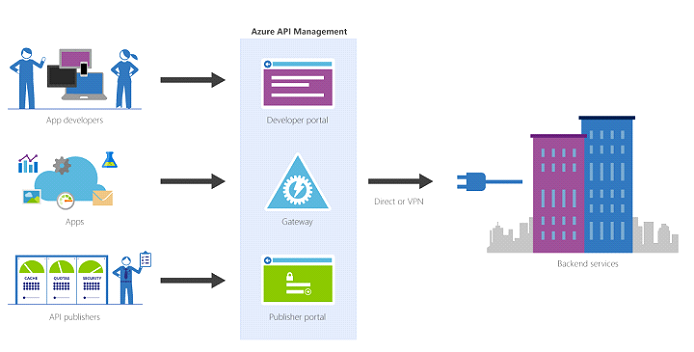
They enable you to visually see and modify records, and they allow you to perform bulk actions such as inserting items into carts.
This can be an effective omnichannel inventory management solution, particularly if you use the Get Multiple by ItemId endpoint.
By using this API, you can get inventory details for catalog items and multiple records. In addition, APIs provide a comprehensive end-to-end view of your inventory across all locations.
3) Use Strong Authentication and Authorization API Solution
It’s vital to implement a strong authentication and authorization API solution as you integrate API with your application.
Without a strong authentication and authorization solution, you’re inviting hackers and threat actors to access your sensitive business data.

While the authentication process is critical, there are also several risks associated with a poor authentication and authorization solution.
For example, improper implementation of authentication and authorization can leave your applications open to attacks by savvy threat actors.
4) Encrypt Traffic With TLS to Secure API Communication
To securely communicate with an API, you must encrypt traffic using TLS. This is accomplished by presenting a server certificate signed by a trusted Certificate Authority.
The certificate contains the public key of the server and the DNS hostname.
It also contains information about the domain’s owner, which verifies that the server is actually the one you are requesting.
It’s not recommended to use self-signed certificates because you must trust the server’s identity. Publicly trusted CAs are the best choice.
5) Use a Web Application Firewall to Secure APIs
If you want to secure APIs, you must implement a web application firewall (WAF) on your server.
Essentially, the WAF acts as the intermediary between the traffic sources and the destination server — as shown
below:
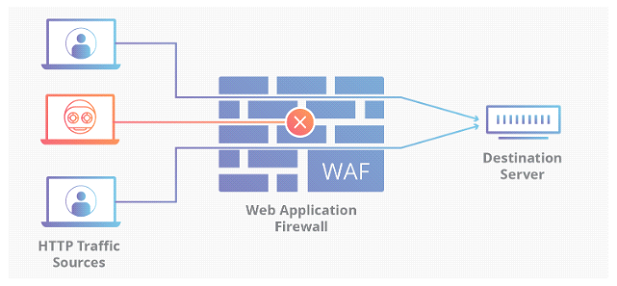
An API gateway is not enough to protect APIs from external attacks, which require more complex security measures.
WAFs integrate with API gateways to provide basic access control for APIs and also include a WAF module.
WAF functionality is particularly powerful because it recognizes common attract strategies and shuts down web-facing service components.
Conclusion
API management is all about adopting an API system that works for your business.
We’re confident that you now have a baseline understanding of what APIs are, the different types of APIs, best practices for designing APIs, and a lot more.
As you harness the right API, you’ll position your business to be able to partner with other applications, such that you can expand your reach, grow your influence, and communicate better with your customers.